The challenges of digital identity
Digital identity allows citizens to access various services on the Internet, both from private companies and public bodies, which require identification for their use. While many companies require identity registration, public agencies often rely on the eID and are responsible for issuing certifications and licenses in different formats, such as ID cards or ID documents.
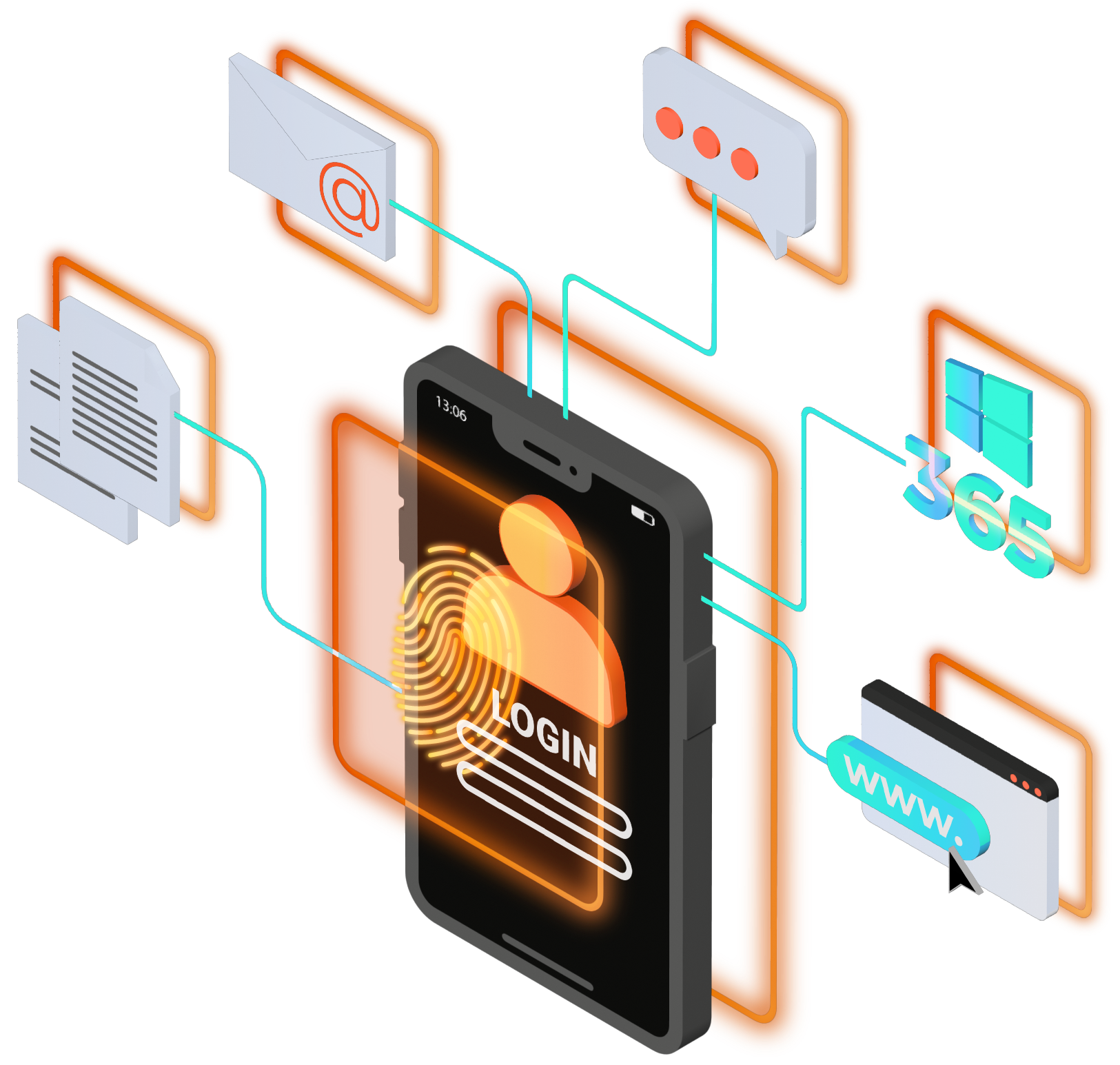
Identity is focused on applications
The first problem is the number of identities we have or have created. Email accounts, online shopping platforms... they all have our data: name, surname, address, etc. Managing these identities for a citizen is an impossible mission. Most of them do not know or do not directly remember where they created these identities. This happens because nowadays identity is focused on applications.
Digital sovereignty
The second problem is that the entire infrastructure to support these identities is based on digital certificates and the entities that issue them. It has become a business and practically the root entities that support such certificate infrastructure are under the umbrella of the USA, a country that decides through its companies which certificates are implemented natively in operating systems, browsers, etc. Nowadays in Spain, the root certificate of our DNIe has to be imported into our browsers manually. This means that the EU is subordinated to this certificate infrastructure and has a digital sovereignty outside the US.
Difficulty of verification
At the same time, as a third problem, a public body may be required to issue certificates to its personnel, whether they are employees or external, proving their relationship with the administration. These documents can be forged and are difficult to verify except by specialized personnel who can validate the information with that of their national identity card.
Vulnerable databases
The fourth problem is that since identity is application-centric, records are stored in databases located in a certain geographical location and can be destroyed in case of catastrophes or cyber-attacks.
Transition between models
The fifth problem is to solve all of the above, but at the same time continue to use the services and provide a transition from the old application-centric model to a new distributed one. Identity lifecycles with their corresponding approvals must continue to be solved and identities must be additionally offered to be associated with digital services.